公式にも通知がありますが、Chanalyzer/Wi-Spy/EyeP.A.などを提供している
Metageek社がクラウド型ネットワーク管理ツールを提供するAuvik社に買収されました。

Metageek社がAuvik社に買収されたことに伴い5月より同社製品販売体制に変更があります。
Wi-SpyAir/Wi-SpyDBxは継続提供OK、Chanalyzerは各オプション廃止で
ReportBuilder機能を含めた単体永続版提供とともに
EyeP.A. TonicととあわせたMetageek Enterprise Suiteとしてサブスク制で提供されます。
詳細は弊社サイトを参考ください
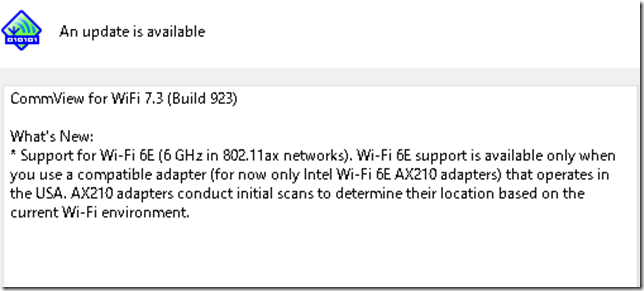
ついにTamoSoft社の無線LAN調査・キャプチャツールのCommView For WiFiが
今回のバージョンアップのバージョン7.3において、Wi-Fi 6Eに対応しました!!
※ただし日本は現在のところ非対応です
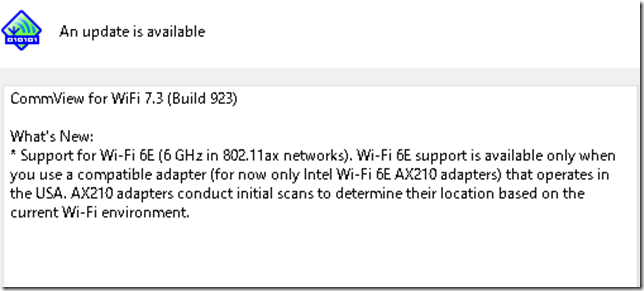
Wi-Fi 6EはIEEE802.11ax(WiFi6)を6GHzの周波数において利用可能とした仕様で
残念ながらまだ日本では認可されていませんが、M.2接続のIntel AX 210アダプタと
組合わせて用いることで米国においてWi-Fi 6Eのキャプチャが可能になります
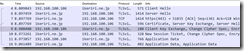
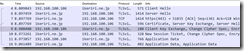
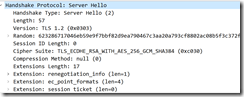
When your TLS server chooses Cipher Suite as TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (0xc030), you can not decrypt Diffie-Hellman key exchange if you have the private key and certification.
In this case, its good way to set SSLKEYLOGFILE from your Browser, Wireshark can decrypt TLS

Create your own NSM devices with Suricata using Dualcomm’s ETAP-PI, network tap appliance
as well as Raspbery Pi with power redundant, graceful shutdown, user defined push buttons and leds.
Youtube movie here
https://youtube.com/watch?v=vo6yySnmvFE
Dualcomm社ETAP-PIで作成するSuricata NSMアプライアンス(日本語・Youtube)
Download PDF
https://www.ikeriri.ne.jp/develop/Dualcomm/Create%20your%20own%20NSM%20devices%20with%20Suricata%20using%20Dualcomm%E2%80%99s%20ETAP-PI,%20network%20tap%20appliance.pdf
Dualcomm’s ETAP-PI is a network tap appliance, there are two gigabit port for inline connection, and 1 monitor gigabit port that aggregate the traffic. Not only network tap, ETAP-PI has a raspberry Pi 4 inside the box. We can create our own NSM ( network security monitoring ), NIDS devices using Suricata, Snort and so on. This TAP appliance has dual redundant power supply and graceful shutdown button, as well as user-defined two LEDs and a push button for enterprise use.
I refer the useful websites below: https://jufajardini.wordpress.com/2021/02/15/suricata-on-your-raspberry-pi/ https://www.reddit.com/r/raspberry_pi/comments/np1a8f/building_my_home_intrusion_detection_system/
Step1: Install Suricata for Raspberry Pi4 Install required packages
apt-get install python-pip libnss3-dev liblz4-dev libnspr4-dev libcap-ng-dev git
Install packages for build Suricata
apt install libpcre3 libpcre3-dbg libpcre3-dev build-essential libpcap-dev libyaml-0-2 libyaml-dev pkg-config
zlib1g zlib1g-dev make libmagic-dev libjansson-dev rustc cargo python-yaml python3-yaml liblua5.1-dev Get Suricata source file
wget https://www.openinfosecfoundation.org/download/suricata-6.0.3.tar.gz Extract source file and change directory for source file
tar -xvf suricata-6.0.3.tar.gz
cd suricata-6.0.3
Execute configure script with some option
./configure --prefix=/usr --sysconfdir=/etc --localstatedir=/var --enable-nfqueue --enable-lua Compile and install Suricata
make
sudo make install Setup rules
cd suricata-update
sudo python setup.py build sudo python setup.py install
cd ..
sudo make install-full
Step2: Suricata Configuration Update Suricata rules
sudo suricata-update Edit configuration file
Nano /etc/suricata/suricata.yaml
Check #ring-size: 2048 section
And uncomment and change ring buffer size to 30000 ring-size: 30000
Step3: Execute Suricata and Test detection
Execute suricata in background ( -c config file -i interface -S rule file)
sudo suricata -c /etc/suricata/suricata.yaml -i eth0 -S /var/lib/suricata/rules/suricata.rules & Check the latest log file
sudo tail -f /var/log/suricata/fast.log Access malware specific website
wget 3wzn5p2yiumh7akj.onio
and you can find alert event like that
ET MALWARE Cryptowall .onion Proxy Domain [**] [Classification: A Network Trojan was detected] [Priority: 1] ps aux | grep suricata to find process ID and kill the process after testing
Step4: Set Suricata as a service Edit service script
nano /etc/systemd/system/suricata.service Copy and Paste a sample
[Unit]
Description=Suricata Intrusion Detection Service
After=network.target syslog.target
[Service]
ExecStart=/usr/bin/suricata -c /etc/suricata/suricata.yaml -i eth0 -S /var/lib/suricata/rules/suricata.rules ExecReload=/bin/kill -HUP $MAINPID
ExecStop=/bin/kill $MAINPID
[Install]
WantedBy=multi-user.target
Start/Stop/Restart/Check Suricata as a service sudo service suricata [start/stop/restart/status]
Step5: Check log and Log rotate
Suricata creates log files at /var/log/suricata
eve.json : huge json file for analysing with Erastic Search and Kibana or Sprunk, etc. fast.log : suspicious event log ( it is useful to just check event )
stats.log : network statistics log
suricata.log : Suricata’s service log
Check the latest suspicious events
sudo tail -n 100 -f /var/log/suricata/fast.log
Suricata may create huge size of log file, so you may configure log rotate setting, so edit log rotate setting file nano /etc/logrotate.d/suricata
/var/log/suricata/*.log /var/log/suricata/*.json {
daily
maxsize 1G
rotate 30
missingok
nocompress
create
sharedscripts
postrotate
systemctl restart suricata.service endscript
}
It means each daily log file limit to 1GB and holds the latest 30 files (for a month) Change logrotate configuration
Sudo logrotate -f /etc/logratate.conf
Step6: Automatically update Suricata rules at midnight
Edit crontab to update and restart suricata at 3:33 am
33 3 * * * sudo suricata-update && sudo service suricata restart
It is a typical setting of maintain Suricata by Raspberry Pi but works best with ETAP-PI
Create and customize your own stable NSM device and be ready for cyber security.
I recommend to connect other packet capturing devices at external port of ETAP-PI.
We can check actual pcap/pcapng file with Wireshark, if you find some important security event!!
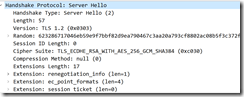
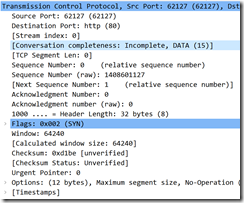
Wireshark3.6.0 tcp.completeness field is a integer value to understand connection state.
the value consists of
1 : SYN
2 : SYN-ACK
4 : ACK
8 : DATA
16 : FIN
32 : RST
when you see the value in your trace file at the Client side, it may be
1: just a SYN(1) packet, the firewall blocked the connection on server side.
3: SYN(1)+SYN/ACK(2), half connection, server is stressful or DoS attaked.
7: SYN(1)+SYN/ACK(2)+ACK(4) just a ESTABLISHED TCP connection without data
so Incomplete, DATA(15) means SYN(1)+SYN/ACK(2),+ACK(4)+DATA(8), TCP connection has been established and start data stream and not finished yet.


![]()



 +
+

